🗓️ Dec 31, 2017 · 2 min read
NOTE: This is completely for experimental purposes and is unsupported by both Apple and VMware
Hello all! This is just a quick follow up to my previous guide on running macOS 10.12 Sierra on ESXi 6.x, where I have now …

🗓️ Dec 31, 2017 · 2 min read
This is an extremely long overdue post, but I have had such a busy year that I really haven’t been able to find much time to write and publish material that I have been meaning to get out. So, as I attempt to get back …
🗓️ Nov 13, 2017 · 3 min read
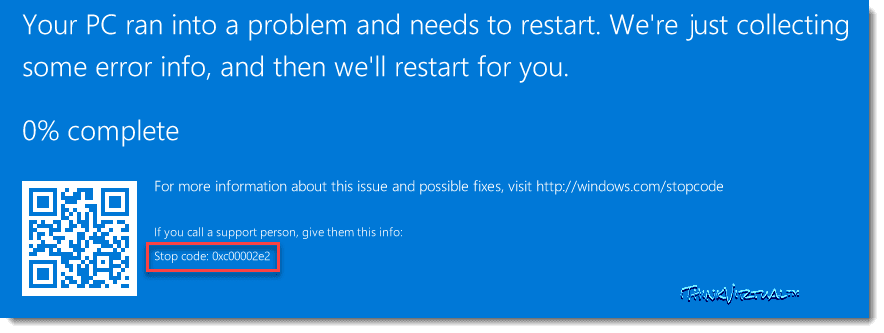
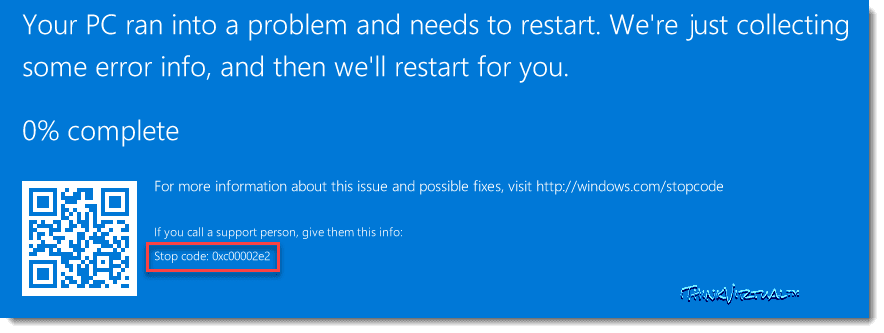
Yesterday morning I discovered that my Synology NAS had an unexpected shutdown in the middle of the night while my homelab VMs/workloads were still running. This caused both of my Domain Controllers databases to become …
🗓️ Mar 27, 2017 · 4 min read
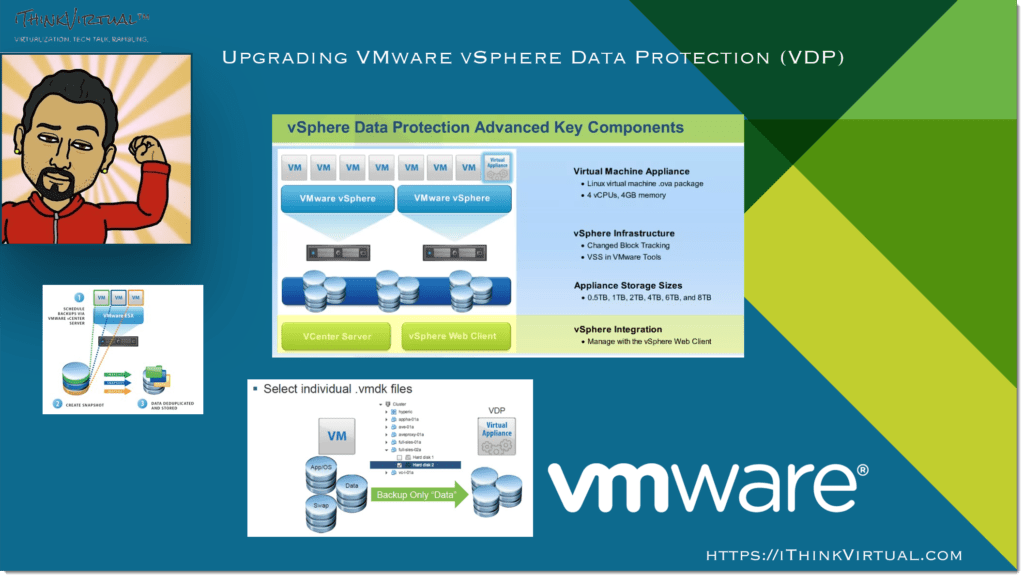
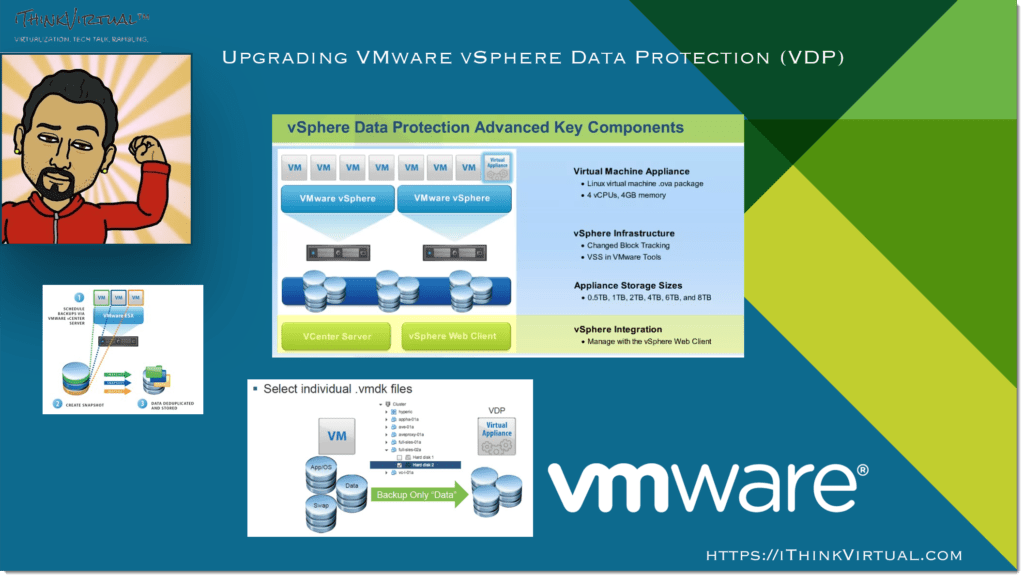
Having a backup solution is imperative in any IT environment, whether it be Production or a simple Home Lab like I have. There are many different brands and companies that offer backup solutions, such as Veeam or Nakivo, …

🗓️ Feb 13, 2017 · 9 min read
Have you ever wondered to yourself, “What is OpenVPN and what is it used for?” I know I have! I currently leverage OpenDNS’s servers in my network, and when I saw that they offer an Open-Source VPN solution, I figured I …
🗓️ Feb 12, 2017 · 6 min read
For the last 6+ months, I haven’t had much time to dedicate to my home lab and overall home network. Between holidays, transitioning to a new employer/role, and everyday life getting in the way, I found that I had to put …

🗓️ Feb 12, 2017 · 7 min read
Create a macOS/OS X VM on VMware ESXi 6.5 & VMware Workstation 12.5.2 Pro NOTE: This is completely for experimental purposes and is unsupported by both Apple and VMware

🗓️ Feb 9, 2017 · 1 min read
Earlier today, I got the notification and I am honored that I’ve been awarded the VMware vExpert 2017 title! The current vExpert count is 1,472 people and this marks my 2nd consecutive year (2016-2017) that I’ve been …